Protecting from ransomware
This section shows you how to protect your computer from ransomware.
Ransomware is a malicious software designed to block access to computer until a sum of money is paid to the attacker. Some of the most notable examples of ransomware are CryptoLocker, CryptoWall, WannaCry and Petya.
Usually, in case of encrypting ransomware, local files are encrypted using a randomly generated key pair that’s associated with the infected computer. While the public key is copied on the infected computer, the private key can only be obtained by paying for it within an allocated amount of time. If the payment is not delivered, the private key is threatened to be deleted, leaving no possible unencrypting method for recovering the locked files.
One of the most common infection vectors relies on drive-by-attacks through infected ads on legitimate websites, but it has also been known to infect via infected downloaded apps.
Ransomware infection can be limited and sometimes prevented with a few best practices:
Use an antivirus solution that is constantly updated and able to perform active scanning
Schedule file backups (either locally on in the cloud), so data can be recovered in case of corruption
Follow safe internet practices by not visiting questionable websites, not clicking links or opening attachments in emails from uncertain sources, and not providing personally identifiable information on public chats rooms or forums
Implement / enable ad-blocking capacities and anti-spam filters
Virtualize or completely disable Flash, as it has been repeatedly used as an infection vector
Train employees in identifying social engineering attempts and spear-phishing emails
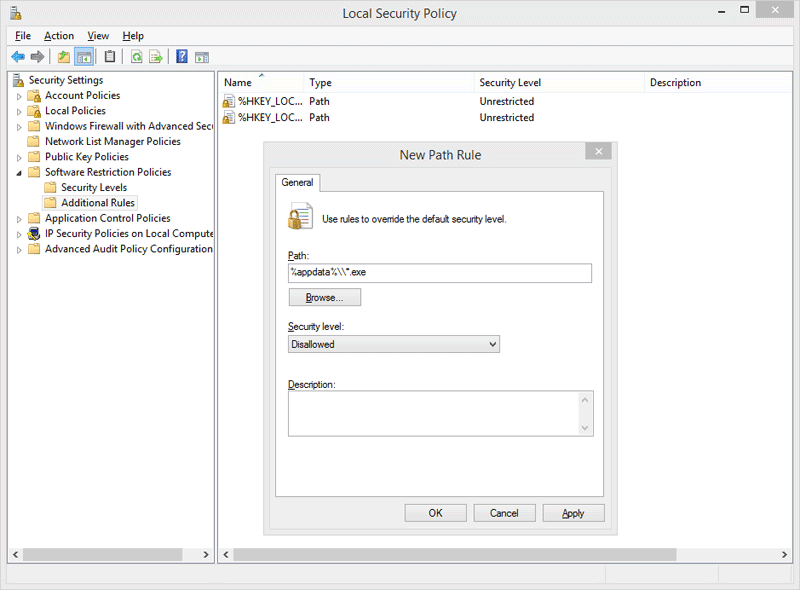
Enable software restriction policies. System administrators need to enforce group policy objects into the registry to block executables from specific locations. This can only be achieved when running a Windows Professional or Windows Server edition. The Software Restriction Policies option can be found in the Local Security Policy editor. After clicking the New Software Restriction Policies button under Additional Rules, the following Path Rules should be used with Disallowed Security Level:
- "%username%\\Appdata\\Roaming\\*.exe" - "%appdata%\Microsoft\Windows\Start Menu\Programs\Startup\\.*exe" - C:\\\*.exe - "%temp%\\*.exe" - "%userprofile%\\Start Menu\\Programs\\Startup\\*.exe” - "%userprofile%\\*.exe” - "%username%\\Appdata\\*.exe” - "%username%\\Appdata\\Local\\*.exe” - "%username%\\Application Data\\*.exe” - "%username%\\Application Data\\Microsoft\\*.exe” - "%username%\\Local Settings\\Application Data\\*.exe”
Identify the network systems which are exposed externally, by running a port scan on WAN IP addresses. Identify which of the network systems are doing port forwarding on those exposed ports.
Secure the following network protocols:
SSH: Root access should not be granted, and authentication should be done through certificates, not with usernames. Only one or two admins should have access to SSH.FTP: Avoid FTP servers with vulnerabilities. Avoid logging in with the usernameAnonymousand without entering a password.RDPandSMB: Disable default user accounts, likeAdminorAdministrator. Allow connectivity only for a limited number of users.VNC: Do not use VNC for remote desktop connections.HTTP:Do not use weak or default credentials.
Frequently scan the installed web services (Django, Python, Java, PHP, WordPress) for any vulnerabilities.
Make sure users do not have access to change any aspect of your site.
Check IoT devices, or any other network devices for vulnerabilities (CCTV cameras, NAS servers, routers) such as weak passwords, vulnerable or outdated software, vulnerable network protocols.
Enforce Two-Factor Authentication (2FA) across your company, including for operating systems.
Constantly monitor network logs for incoming external connections and block those IPs in your firewall.
Users should only have access to the resources they need. Be especially careful when granting them write permissions to resources.
Limit access to the network shared folders based on business need.
Disable administrative shares.
Network administrators should monitor systems in real time for any suspicious behavior, like high CPU usage.
Block access to
wevtutil.exeandvssadmin, to prevent users from deleting system logs or system back-ups.
Engaging Bitdefender Enterprise Support when infected with ransomware
In case you require help with recovering your files, following a ransomware attack, you can contact Bitdefender Enterprise Support.
Bitdefender will perform an analysis, identify the strain of ransomware, and try to provide you with a decryption tool.
Keep in mind that developing a decryption tool for a specific sub-type of ransomware is usually a lengthy process that has a low chance of success. However, if we do succeed in creating it, we will ensure to make it available immediately on Bitdefender Labs page.
To conduct a proper investigation as quickly as possible, provide the following information:
BDSysLog. Learn how to create a Bitdefender System Log here.
Support Tool log. Learn how to create a Support Tool Log here.
The ransom note that was generated after the encryption. This is usually a .txt file.
Windows Event logs. You can find these logs in
C:\Windows\System32\Winevt\Logs.A couple of encrypted samples. If possible, a pair of encrypted and unencrypted files.
Estimated date and time when the attack occurred.
Other information about the attack that you think is relevant.
While our AM team is working on recovering your encrypted files, you should restore the systems in your infrastructure from your backups.
Take these emergency actions as soon as you’ve been attacked:
Change the users’ passwords.
Change the admin accounts to non-admin accounts if they are not needed.
Disable the administrative shares.
Allow RDP access only for the endpoints that need remote access.
If we are able to recover the encrypted files, you will need to:
Restore your entire infrastructure, whilst keeping the encrypted files and ransom-notes in their original location for the decryptor to run.
or
Restore the OS by moving the encrypted files and ransom notes on a backup, so we can run the decryptor there.
In the unfortunate case when we cannot recover the encrypted files, you should restore your system’s infrastructure from your backups.
If a VM in your network is infected and the attack is ongoing, you need to isolate the VM, suspend it, power it off or force user logout.
Pay attention to specific behaviors that a ransomware attack presents. The ransomware process will be consuming a large amount of the CPU resources.
Pay close attention to the users in the network, as the user impersonated by the attacker will have a weird behavior.
Use a custom application that works alongside the ransomware protection app. This application will:
Shut-down the system when a process is consuming a large amount of CPU resources (>70%).
Send a notification to the IT Admin regarding the CPU excessive load which will include the app name that is using the extra resources and the name of the virtual machine which used the resource.
Shut down the system when the product is no longer protecting your environment (no longer running on that machine - latest security content update has more than 2 hours or the main process
epsecurityservice.exeis not running).Deny the execution of any application except for some frequently used apps.