Configuring single sign-on using a 3rd party Identity Provider
GravityZone Cloud supports single sign-on (SSO) with 3rd party Identity Providers (IdP) that use SAML 2.0, such as AD FS, Okta and Azure AD.
Important
GravityZone SSO has been officially tested with AD FS, Okta and Azure AD, but it can also work with other Identity Providers using SAML 2.0. This topic includes general information about configuring the Identity Providers and links to dedicated procedures for configuring AD FS, Okta and Azure AD.
If GravityZone SSO fails with another Identity Provider than those officially supported, this can happen because of that specific Identity Provider settings. Contact the Bitdefender Enterprise Support for possible recommendations. However, while we do our best to help you, the recommendations are not guaranteed to work for all Identity Providers.
Important
You cannot use at the same time single sign-on (SSO) and two-factor authentication (2FA) in GravityZone.
Overview
GravityZone single sign-on allows users to log in to Control Center by authenticating with an identity provider, as a simpler and more secure method than GravityZone credentials, as users do not need to remember or renew their passwords.
GravityZone supports service provider (SP) initiated single sign-on, which implies the following user authentication flow:
Users go to https://gravityzone.bitdefender.com/, enter their emails, and click Next.
GravityZone creates a SAML request and forwards the request and the users to the Identity Provider, asking for authentication.
Users authenticate with the Identity Provider.
After authentication, the Identity Provider sends to GravityZone an authentication response in the form of an XML document signed with an X.509 certificate. The Identity Provider redirects users back to GravityZone.
GravityZone retrieves the response and validates it with the certificate fingerprint, allowing the users to log in to Control Center with no other interaction from them.
As long as users have an active session with the Identity Provider, they continue to automatically log in to GravityZone Control Center.
Prerequisites and requirements
To enable GravityZone SSO, the following conditions are required:
You have a GravityZone Cloud administrator account to manage users, your company and other companies.
You have an account with an identity provider (AD FS, Okta, Azure AD etc.) to configure single sign-on.
GravityZone users have accounts with their Identity Providers with the same email addresses.
Important
As GravityZone administrator, you can configure single sign-on for users from your company and from companies under your management. You cannot enable SSO for your own GravityZone account due to security reasons.
Users must be under companies that have SSO enabled. While SSO is active, users cannot log in with GravityZone credentials.
Email addresses are case sensitive with GravityZone SSO. Therefore, username[at]company.domain is different from UserName[at]company.domain and USERNAME[at]company.domain. If the email address from GravityZone does not match the email address from the Identity Provider, the user will receive a login error message when trying to connect to Control Center.
Configure GravityZone SSO
To enable GravityZone single sign-on, you must do the following:
Configure the identity provider
Configurating single sign-on may vary from one identity provider to another. However, Identity Providers require almost the same elements to integrate with GravityZone:
Single Sign-on URL – the location where the SAML assertion is sent with a HTTP POST. Also known as Assertion Consumer Service (ACS) URL. For GravityZone, the single sign-on URL is
https://gravityzone.bitdefender.com/sp/login.Service Provider Entity ID – The application unique identifier that is the intended audience of the SAML assertion. Also known as Audience URL. The Entity ID for GravityZone is
https://gravityzone.bitdefender.com/sp.Name ID format – refers to the format supported by the identity provider. Service and identity providers communicate with each other using a name identifier related to a user. For GravityZone, the name ID format is
emailAddress.Single Logout URL – the location where the logout response is sent. For GravityZone, the single logout URL is
https://gravityzone.bitdefender.com/sp/logout.Service Provider Issuer – this is usually the Entity ID and the service provider use this information for verification. For GravityZone, the single sign-on URL is
https://gravityzone.bitdefender.com/sp/login.
You can find these elements in the GravityZone metadata URL document: https://gravityzone.bitdefender.com/sp/metadata.xml.
For your company, the GravityZone metadata URL is displayed in the My Company > Authentication page in GravityZone Control Center.
For a company under your management, the GravityZone metadata URL is displayed in the company details from the Companies page.
For details on how to configure certain Identity Providers, refer to this topics:
Enable SSO in GravityZone
After configuring the Identity Provider, go to GravityZone Control Center to enable SSO for companies and users. Only users under a company with SSO enabled have the option to log in with an Identity Provider.
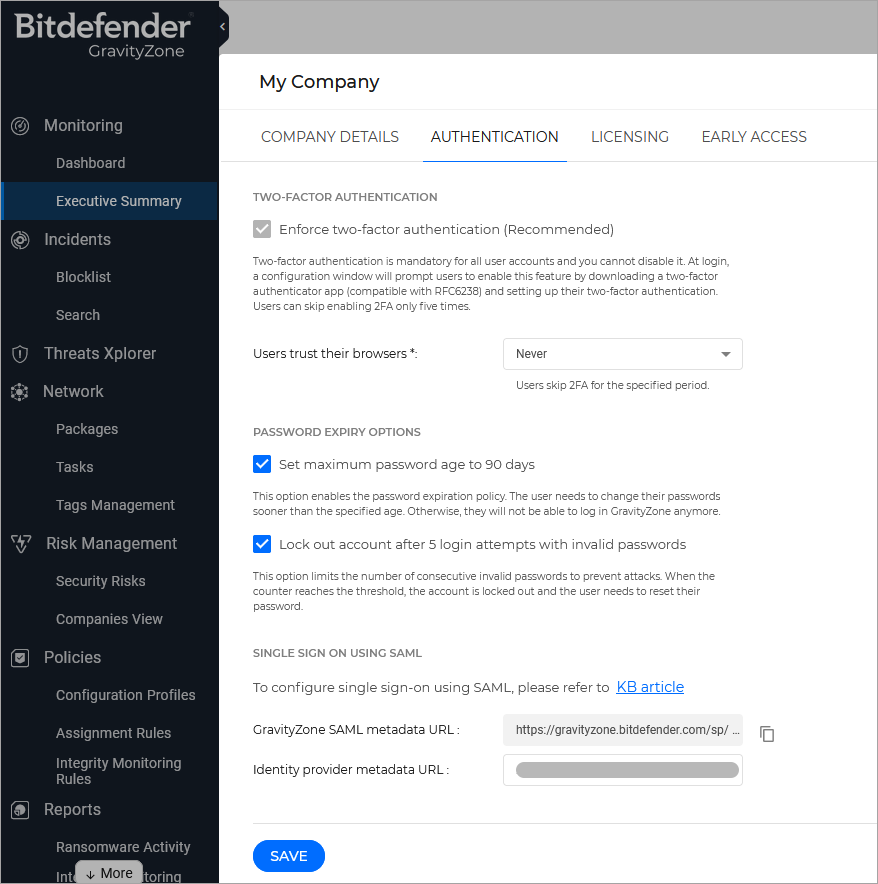
Enable SSO for your company
This is how you enable SSO for your company:
In the upper-right corner of Control Center, go to Welcome, [your username] > My Company.
In the Authentication tab, under Single Sign on using SAML, enter the Identity Provider metadata URL in the corresponding field. The other field, reserved for the GravityZone metadata URL, is non-editable.
Click Save.
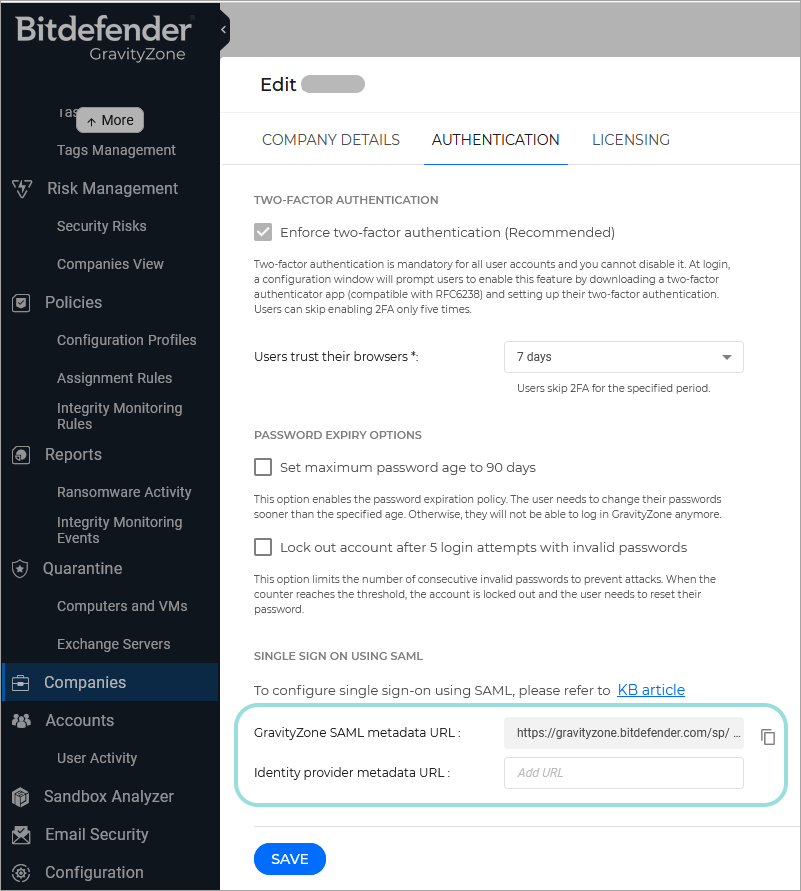
Enable SSO for managed companies
This is how you enable single sign-on for a company under your management:
Go to the Companies page.
In the table, click the company’s name.
Under Configure Single Sign-on using SAML, enter the Identity Provider metadata URL in the corresponding field. The other field, reserved for the GravityZone metadata URL, is non-editable.
Click Save.
Change the authentication method for users
After enabling SSO for a company, GravityZone user accounts under that company become available for changing their authentication method.
You can change the authentication method for users one by one, as follows:
Go to the Accounts page.
In the table, click the user’s name.
Under Settings and Privileges, go to Authentication method and select Login using your Identity Provider.
Click Save.
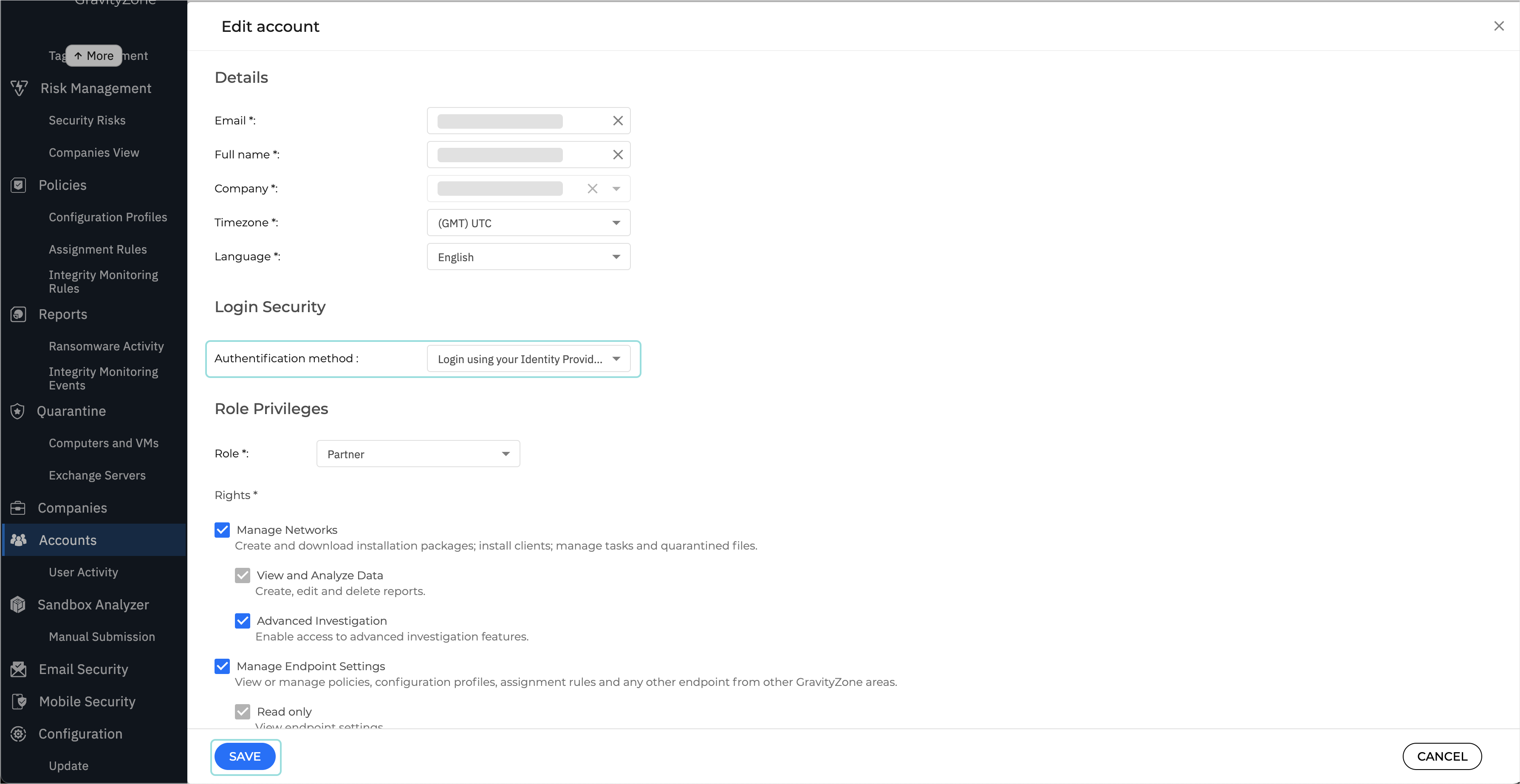
You can enable SSO for as many GravityZone users as you want, but not for your own administrator account.
Note
If the configuration page of a GravityZone user account does not display the Settings and Privileges section, then probably the company has not SSO enabled.
Test GravityZone SSO
After configuring both the identity provider and GravityZone, you can test single sign-on as follows:
Log out from GravityZone.
Log out from your identity provider (AD FS, Azure AD, Okta, etc.).
Enter a valid email address created for testing (other than the one of your GravityZone administrator account).
Click Next.
You should be redirected to the Identity Provider's authentication page.
Authenticate with your identity provider.
You will be redirected back to GravityZone and, in a few moments, you should automatically log in to Control Center.
Disable GravityZone SSO
To disable single sign-on for your company or for a company under your management:
Delete the Identity Provider metadata URL from the configuration page of that company.
Click Save and confirm the action.
Users can obtain new passwords by clicking the Reset my password option on the Control Center login page and following the instructions.
To re-enable GravityZone SSO for a company, enter again the Identity Provider in the configuration page and click Save.
After re-enabling SSO, users under that company will continue to log in to Control Center with GravityZone credentials. You have to manually configure each account, one by one, to log in with the Identity Provider again.